PCI-DSS Compliance Checklist [Definition + 13 Steps]
Day-to-day business is complicated enough for new e-commerce site owners, but if you accept debit or credit card transactions, one crucial part of your remit is to be completely compliant with the Payment Card Industry (PCI) standards.
This can feel overwhelming as the PCI DSS compliance checklist is long, can seem complicated, and more often than not raises more questions on PCI security standards than it answers.
In 2018, more than 1.3 billion personal records were stolen according to Privacy Rights Clearinghouse, so it is clear that these types of rules are essential for secure processing.
This is a brief overview of the Payment Card Industry Data Security Standard (PCI DSS) and it answers the common questions that come up for new e-commerce owners.
But it can also help software developers who have a responsibility to adhere to best practices so that their solutions can be made easily compliant.
I. What is PCI DSS Compliance?
PCI Security Standards Council defines PCI DSS as a set of data security standards that companies should follow if they use debit or credit card information in any way to ensure a secure data environment.
Initially designed by the major credit card brands including Visa, MasterCard, Discover, and American Express in 2004, the PCI DSS checklist is now used by millions of online sellers from all over the globe to protect their businesses against cyber attacks.
The first step to following these requirements is to understand what credit cardholder information you have, where it is stored and how it is protected. To do this the PCI recommend three distinct actions you must take:
- Assess your data and processing
- Remediate any vulnerabilities
- Create reports on both the remediation carried out and compliance
As a starting point, this is a broad PCI compliance checklist of how to implement PCI DSS but when carrying this out e-commerce owners, particularly those new to the standards, often have the same questions.
II. What Is the Scope of PCI DSS?
This stage involves determining and defining your cardholder data environment (CDE).
You have to establish exactly what parts of your system are concerned with storing, processing or transmitting either cardholder data or any related sensitive payment authentication data.
Although this generally relates to your IT infrastructure, your CDE will also take into account people and processes as well as technology. The technology aspect will normally cover virtual and real network devices, servers and applications — internal or external.
Establishing exactly what part of your systems is covered by the PCI DSS should be carried out at least once a year, and always prior to your annual assessment.
Once the CDE has been identified, any vulnerability must be analyzed and fixed. PCI compliance reports must also be verified for accuracy and if any vulnerability was found, validation reports must be created to prove the fix.
Please note that SSL certificates on their own will not ensure PCI DSS compliance as extra safeguards on top of this will be required. They won’t restrict access to cardholder data, keep sensitive authentication data secure, and protect cardholders from data breaches.
1. What about My Wireless Networks?
Almost any systems these days have a wireless component. For e-commerce this could be:
- any point-of-sale device
- hand-held scanners
- your website if you are connecting to the internet anywhere via a wireless router or server
- any other type of line-busting technology
As payment card information will be used or stored by these devices, they will all become part of your CDE and included in PCI DSS compliance.
If you only take credit card numbers over the phone or you don’t actually store any card data but just use it for payment purposes, these standards will be easier to navigate but they still apply to you.
Ideally, only non-sensitive data would be used wirelessly as it is infinitely easier to comply with the standards in this case.
However, where this is impossible, the PCI
2. What about Third-Party Service Providers?
There are two issues here:
- using third-party payment processors;
- using a company as an outside resource to manage your PCI compliance.
Firstly, the use of third-party payment gateways does take away some of the risk exposure and therefore this results in less work required to ensure compliance. However, it doesn’t completely negate any responsibility, and an e-commerce business still has to be compliant with its remaining CDE.
It is advisable to draw up a contract that both companies agree to, and this can take the form of two alternative services.
- The third-party company can prove their PCI compliance by having an independent annual assessment carried out and provided to you.
- Or else, they can do their own assessment, but the contract must state what PCI compliance needs are to be met so that you are completely covered.
3. Is Network Segmentation Advisable for PCI-DSS Compliance?
Network segmentation is not part of the standards and it is not necessarily required to be PCI DSS compliant. However, as network segmentation could isolate the CDE from any other part of your IT infrastructure, it is an excellent way to reduce the overall scope as well as reducing cost, risk and the associated difficulties with implementing the standards.
A system that does not involve segmentation results in every part of your network being part of the scope of these standards. Therefore, every single part of your network has to be reviewed and made compliant whether it uses and stores sensitive payment card data or not.
This obviously can result in far more work than is necessary, and if you can separate out your core CDE and segment it from the rest of your systems it will make PCI compliance a much more straightforward and simpler process.
You can separate your CDE from the rest of your infrastructure by utilizing internal firewalls or keeping specific sensitive information on special routers that are not connected to any other part of your network.
The idea is to keep the data you hold about your customers’ credit cards in as few locations as possible, then only those areas need to be reviewed and made PCI compliant.
This is a simple issue if the IT design has been written with
In these situations, the analysis will need to establish whether it would be more efficient to segment and have a smaller subset of systems to make compliant, or to keep the systems as they are and run compliance for the whole network.
If network segmentation has been chosen, then for PCI compliance you will need to show proof that your CDE is truly isolated and meets all PCI standards.
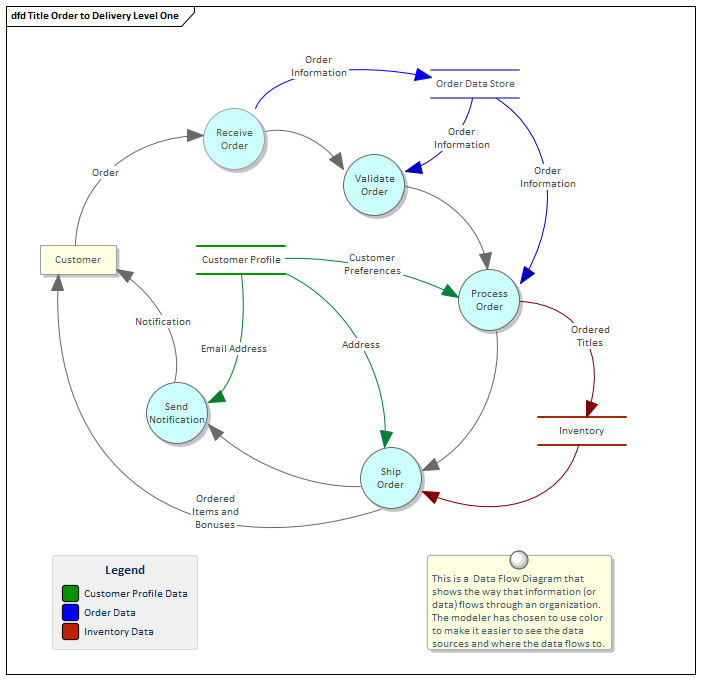
Source: Sparx Systems
A dataflow diagram (you can see it on the picture above) can help to document this as you need to verify that all the parts of your network that store, process or transmit cardholder information are indeed separate from the rest.
IV. PCI DSS Compliance Best Practices in Day-to-day Business
As much as compliance with PCI DSS seems to take you away from your real job of making your e-commerce business a success, it is vital not only to avoid the fines but for keeping your company in business.
When a firm has been affected by a security hack and sensitive info has been stolen, it can spell disaster for the company concerned. Loss of customer confidence and doubts about your reliability can see downturns in sales and ultimately even cause you to go out of business.
Rather than treat compliance as a necessary evil once a year, a culture of continual PCI compliance will firstly stand you in good stead for the annual reviews but will also protect and secure your company on a day-to-day basis.

The PCI has recommendations for making your business continually compliant and ensures the business is meeting PCI standards:
- Develop and maintain a secure network, systems
and applications. - Encrypt the transmission of cardholder data across open and public networks.
- Monitor all-access. Track and monitor network resources and cardholder data access, and ideally use system activity logs to link each user with a specific activity while creating audit trails.
- Create a disaster recovery plan so that in the event of a problem you already have to hand the processes you and your staff need to follow. These processes should enable you to restore control quickly, find the reason for the failure or incursion, and resume normal business as soon as practicable.
- Review all changes that may affect your CDE timely. If you are making changes to your IT infrastructure that in any way connects to your CDE, make sure that all the changes are reviewed and the impact on your compliance is risk assessed. If any PCI DSS requirements are affected by your IT changes the new scope must be noted, and you must ensure that any new vulnerability is fixed with the associated reporting requirements.
- Mergers and acquisitions can also make a difference to the scope of your PCI compliance, so a review of the impact on each occasion is advisable.
- If you deal with any companies or individuals in the European Union, ensure you also comply with GDPR as well as PCI DSS data protection.
- Protect stored cardholder data using strong passwords, locked servers, authentication protocols, locked storage cabinets, you name it.
- Regularly test your security systems and processes to ensure everything is working as needed.
- Maintain an information security policy for all your employees.
- Do not use vendor-supplied defaults for passwords and other security settings.
- Install anti-virus software and ask your colleagues do the same.
- And, no need to mention that, you must restrict physical access to cardholder data.
If you can continually monitor all changes in this way, you have a much better chance of protecting sensitive card data and your company at all times.
If you can also add occasional ad-hoc reviews to make sure employees are following this PCI compliance checklist ensuring that you are continually compliant, you can catch any failings before they become an issue.
Who is a Qualified Security Assessor (QSA)?
A QSA is registered with the PCI as being qualified to assess and validate a company’s compliance with the PCI DSS.
They often work for standalone QSA companies and can help a large company find any gaps in their data security when they transmit cardholder data and helps identify and eradicate any vulnerability.
Can I Ask a QSA to Use Samples to Make Sure My Business Is Compliant?
If your company is large or maybe spread over many different locations, it may not be advisable to have a PCI DSS audit carried out in its entirety over the whole of your business. You cannot make that decision yourself as a QSA should be the one to decide to choose a sample of your business to review, but there are restrictions.
It is not a shortcut to compliance, the organization must be thoroughly compliant at all times to all PCI standards and have the required documentation, technology and reporting in place to ensure and verify this compliance.
The QSA will not simply review a small part of your environment or a small number of requirements, rather they will choose a sample of all the locations where the payment information is stored and then a sample of the system components used there, marking down their PCI compliance checklist as they review.
Having a standardized PCI DSS compliance process and methodology that all employees follow, means that fewer locations need to be selected for compliance testing. If all locations are treating compliance differently, every alternate method will need to be checked which may result in your whole organization being assessed regardless.
What is a Compensating Control and Can I Use It?
A compensating control can be used if it is not possible to follow the PCI DSS compliance rules as described.
It must not be used as a shortcut, however, as there must be a legitimate business reason for it. There are very strict criteria that must be met before control is accepted, as security must be equal to or surpass the original requirement.
They can be difficult to verify so if you can do without them you should.
Next Steps
If you are new to e-commerce, matching the PCI DSS compliance rules may seem an uphill struggle.
If you can review the information in the standards and establish exactly where your company stores payment card data and how you process it, you will be well on your way. While considering the standards, make sure the pointers in this list are adhered to and remember to review your PCI compliance checklist each year along with any compensating controls you may have put in place.
Once you have an accurate knowledge of your CDE and have closed any loopholes or vulnerabilities in your site’s PCI compliance, you can be sure that you are protecting your customers’ data securely.
eCommerce fraud is unfortunately widespread, but the more we can do to stop the hackers and thieves the safer we will all be.
Have you already created a PCI DSS compliance checklist for your eCommerce business?
About the author